How to Protect Your Phone from Viruses and Malware?
Nowadays most of us are doing our primary digital jobs on a smartphone or it can be said that in another way smartphones are our primary devices for our day-to-day activities.
But most of us are not careful to protect our devices (not hardware protection) until a virus attack or malware damages our phones. Here we are describing how to protect your phone from viruses and malware.
Will Virus Affect Phones?
Phones may become infected with viruses. As smartphones’ popularity surpassed that of desktops as personal devices, hackers devised new methods to infect and harm them.
Unlike previous viruses that multiplied themselves while running, mobile malware and viruses target weak places in your operating system for data mining, financial gain, or network damage.
Data-sharing capabilities are normally banned amongst programs, but certain apps have been inspected for suspicions of data abuse, rendering their users more exposed to these sorts of assaults.
What Is Malware?
Mobile malware is virus code for Android or iOS specifically designed to attack smartphone systems.
These kinds of malware depend on exploits of specific operating systems (OS) or mobile phone software technology and vulnerability in the mobile applications we are using.
Some types of smartphones are targeted more frequently than others within the general category of mobile malware.
Industry study demonstrates that an overwhelming majority of mobile malware targets the Android platform rather than other common mobile OS such as iOS from Apple.
Different types of mobile malware include device information thefts and device spies that take certain types of information and send it to hackers.
Another form of mobile malware is called root malware, or malware rooting, which provides hackers with some administrative privileges and access to files.
Other types of mobile malware are also available that conduct automatic transactions or communications without the understanding of the device holder.
One feasible alternative is to upgrade to the latest OS version to limit the potential for mobile malware.
Users can also search for data from the smartphone maker about how it handles mobile viruses, malware, and OS updates.
Difference Between Malware and Virus
The distinction between malware and viruses appears to be a general misunderstanding among internet users. The two terms are frequently used interchangeably and this is completely okay to some extent.
Malware is a mix of “malicious” and “software” phrases. It relates to software that is malicious on exploited systems.
There is malware for computers and malware for the website. Web-based malware is malicious software that infiltrates a website or database system.
Web-based malware can be an online system targeting malware, such as a computer operating system or software application. That’s why there are distinct goals for computer malware and website malware.
A virus is often used as a “malware” synonym, but it relates technically to a particular form of malware.
A virus, depending on its goal, can infect anything from a computer to a mobile device, to a website.
Different Types of Mobile Viruses
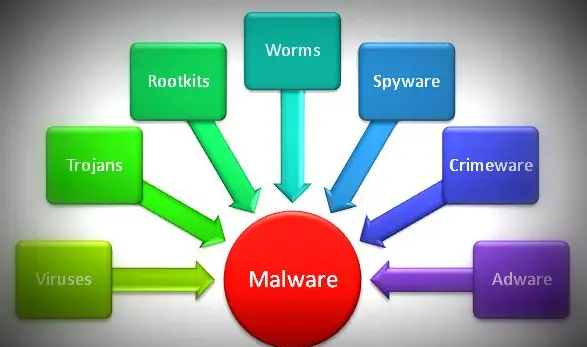
Before knowing how to protect your phone from viruses we should know the different types of malware work in somewhat various ways.
To know about different types of computer viruses you may read this also: Do You Know About Different Types Of Computer Viruses?
Most of these computer viruses have their mobile version also. Each of these virus programs is written to attack a specific operating system.
Malware programmed for attacking Windows systems can not do anything on Android systems in most cases and vice versa.
Each type of malware has its own specific identity of attack. Here’s a summary of some of the most popular malware types:
- Virus
- Worm
- Trojan
- Scare ware
- Spyware
- Adware
- Ransomware
What Does Malware Do to Your Phone?
Malware has traditionally been aimed at generating income.
It can steal your data, send SMS to premium text services on your phone, or install adware that will force you to view or download web pages.
Mobile malware attacks as info stealers can steal your contact list, personal details, location, passwords, etc.
Cybercriminals can access your devices with the help of malware and steal your information for their use or sale on the dark web.
Hackers also use ransomware to lock phones and encrypt private information and then request a victim’s ransom payment to get back access to their records.
How a Virus Entered a Mobile Phone?
As you know the mobile phone is a computer with some other additional features and hence it is called a smartphone.
So in most cases, malware is inserted into your system with some mobile applications, email attachments and other files that are intended to do so.
So in the case of our computer malware protection, we have to do smartphone malware protection too.
How Do You Know If Your Phone Has a Virus?
A lot of readers are asking ‘How do I know if my phone has a virus?’
We would like to answer that there’s no ideal phone. They may be susceptible to external as well as internal harm. While the external damage is generally noticeable, it may be possible to hide inner harm in plain sight.
Take, for instance, malware. As explained earlier it is software that is malicious and can squeeze into your phone.
Written to cause damage, malware involves worms from computers, Trojans, ransomware, and spyware.
While many malware just limits your phone’s functionality, others are designed to steal and erase data, distribute malware to other devices, or make illicit transactions.
Because mobile malware can remain dormant while you use your phone normally, you may not realize you have a virus right away.
Furthermore, certain inferior performance concerns are natural indications of phone use. These symptoms, however, might also be an indication of harmful software at work.
It is known that malware performs repeated duties that take on your phone a lot of resources. Malware on mobile phones sign may appear as follows:
- Your phone is too slow: Malware may quickly eat RAM and CPU, causing your phone to function slowly and overheat. While occasional overheating may be natural, a recurring problem might be an indication that there’s something more alarming happening.
- Apps take more time to load or App crash: If your mobile software is hacked, apps may crash constantly. Check that your storage isn’t full and that you don’t have too many applications operating at the same time before looking for a virus and expecting the worst.
- The battery drains faster than normal: If a virus is running in the background, you may notice an unusually rapid drain on your battery due to increased usage of your phone’s RAM.
- There are too many pop-up ads: When some pop-ups are a regular function of advertising while browsing the web if your browser is closed and you’re still getting pop-ups, you may be dealing with adware, a sort of malware whose objective is data mining.
- Your phone has apps that you haven’t downloaded: Unrecognizable or fraudulent applications that were strangely downloaded may be a harmful kind of infection. Trojan horses can potentially infiltrate legal apps and do more harm.
- Huge data usage and big phone bills: Unidentified viruses that operate in the background of your phone might substantially boost data use. Some trojans may increase your phone bill by charging you for in-app purchases and text messages to premium accounts, which hackers may then collect on.
How Can Check The Phone For Viruses?
An antivirus scan is a nice way to mobile malware detection on your Android phone.
Before purchasing your phone’s antivirus software, make sure you select the most extensive item available for your device.
There are many free and premium antivirus software solutions (View on Amazon) for Android available on the market to ensure your phone has no viruses. But for iOS no good antivirus software is prevalent.
Even though it is very difficult to find the best Android security app, Kaspersky Internet Security for Android (View On Amazon) is the best antivirus for Android mobile, as we experienced in our research.
Do your studies to guarantee a full scan runs the cybersecurity application you invest in and does not ignore any vulnerabilities.
An incomplete scan may give you a false sense of security, making your device vulnerable to cyber-attacks which may adversely affect our intention to protect your phone from viruses
How Can We Remove Malware from a Phone?
The most significant thing to do if you believe you have malware on your phone is to prevent the malware from causing any further harm.
You can take a few measures to assist in minimising further losses here.
- Restart the phone in safe mode. Press and hold the power button. Most Android devices come with the Safe Mode option to restart.
- Uninstall the app you suspect. In Settings, find the app and uninstall or force it to close. This may not remove the malware entirely, but further harm may be prevented.
- Look for other applications that you believe may be infected. There is a strong possibility that the malware might have infected some applications. If you feel that in that way remove those applications also.
- The better thing is to scan your device with good anti-virus software which can take care of it up to a certain extent and can be used as a mobile malware removal tool.
Related: Speed up Android phone with hidden system settings in Android
How Can You Protect Your Phone from Viruses and Malware?
For protecting your phone from viruses, malware, or any other potential cyber-attacks, some suggestions are provided below.
- Invest in Top-Notch Security for Your Android: To escape from future threats, invest in a decent security suite to safeguard your Android device from malware. Apps can sometimes include dangerous code. When you download them, the code is transmitted to hackers, rendering your device unsafe. Install reputable antivirus software to avoid this. Further, antivirus applications provide further security by wiping your data if your device is lost. It monitors unfamiliar calls and threats, deletes cookies, examines browser history, and alerts you to malicious risks.
- The Importance of Regular Updates: Stick to the updated versions of all operating systems and other application software. Remember that your mobile device’s firmware might potentially be vulnerable to security risks. To identify new threats, keep your device firmware updated at regular intervals (manually or automatically). Main mobile device firmware companies, such as Google Android and Apple iOS, provide new updates regularly to safeguard your device’s vulnerabilities.
- Navigating Suspicious Links and Frauds: Avoid clicking on suspicious links in emails and text messages. Be cautious of social engineering frauds. Cybercriminals like impersonating banking applications, sending false SMS designed to acquire personal information and sending harmful links and files via email. View any messages from unfamiliar sources with caution, just as you would on your computer. If anything appears to be suspicious, it most often is.
- Strengthening Your Device’s Defenses: Use complex passwords for your device and applications. Strong passwords combined with secure biometric features such as fingerprint authenticators eliminate 90% of illegal access. With this safeguard, external access is almost impossible. Don’t ignore the two-factor authentication for further security. Remember that your password must be complicated, using a combination of characters, numbers, and alphabets. Change your passwords at least once every six months.
- Protecting Your Data on Public Networks: Never use unsecured public Wi-Fi connections. Everyone has access to free WiFi, and malicious people spy on network communications. When you connect to free WiFi, they eventually obtain your account, password, and any critical information. Also, connect using WPA (WiFi Protected Access) rather than WEP (Wired Equivalent Privacy). When not in use, turn off WiFi and Bluetooth. If necessary, when connecting to public Wi-Fi, it is better to use a VPN.
- The Role of Cybersecurity Suites: Always use a powerful cybersecurity suite on all Internet-connecting devices.
- Safe App Installation Practices: Always install applications from the Google Play Store or Apple’s app store and avoid external untrusted sources. To know how much access you give to the apps, read the fine print and permissions on the applications. Avoid downloading bogus applications that imitate the logos of well-known companies.
- Safeguarding Your Privacy in Apps: Check App permissions: Read the terms and conditions of any unfamiliar app before downloading it or allowing it to connect to other applications in your digital world. Permission to access personal information, including contacts, or to modify the conditions without notice should never be granted automatically.
- The Dangers of Rooting Your Device: Don’t jailbreak your phone: Staying rooted lets you install required operating system updates and fixes as they become available. When you jailbreak your phone, you expose it to vulnerabilities present in prior versions as well as the risks that open-source code might provide.
- Ensuring the Safety of Your Information: Back up your phone’s data. Consider linking your device to the cloud service associated with it to automatically backup (and encrypt) data. If you don’t trust the cloud, make sure you connect to a PC or Mac regularly to sync data to preserve pictures, videos, applications, and other items.
- Securing Your Connection in the Digital Wild: When using free Internet access, a VPN allows you to connect to a secure network. VPNs are also useful when you need to access sites with minimal security. However, avoid non-HTTPS websites. They’re vulnerable to man-in-the-middle (MITM) attacks.
Some smartphone viruses remain inactive until they are triggered, to invade as much user data as possible before being noticed.
Antivirus software may safeguard your mobile devices from cyberattacks, and installing an Android VPN on your device can provide further security against the instabilities of open-source code.
Maintain caution while installing new software on your devices, and be aware of any performance concerns that may be related to mobile malware symptoms at work.
We hope you are interested in this article and please share the same with your friends and relatives.
Subscribe to our free newsletter so that you will get regular updates directly in your Email.
Also, consider following our Facebook and Twitter pages for regular updates
Disclosure: If you follow the links in this article to a retailer’s website and make a purchase, we will get an affiliate commission on some, but not all, of the items or services we promote without affecting your price.