15 Types of Computer Virus And How Can Avoid Them?
Computer viruses are more widespread than ever due to our increased reliance on technology and the internet in our everyday lives.
Computer viruses are malicious software programs that penetrate, infect, and disrupt computer systems, resulting in substantial data, privacy, and general functioning destruction.
Understanding the many forms of computer viruses is critical for protecting ourselves and our electronic devices from danger.
In this post, we will look at 15 different types of computer viruses and discuss practical ways to prevent being a victim of their destructive abilities.
Definition of a Computer Virus
Sometimes a computer virus is more dangerous than a bio-virus. What is a virus on a computer?
The VIRUS full form in computer terminology is said to be Vital Information Resources Under Seize.
It is nothing more than a program coded for malpractice that can interrupt a computer system’s functioning.
These viruses can infect the host computer and, in multiple harmful ways, alter its workings.
They can steal information, delete or alter documents and files, steal or harm hard disk spaces, or cause a software program to work in an unwanted way.
Other damaging activities of these viruses include attaching to disk files, email attachments, USBs, and hard drives. Different types of viruses can slow down the processing of your CPU overall.
The computer virus replicates itself by changing computer programs and is transmitted to other PCs and devices by transferring infected files, emails, disks, and USBs.
Once these are opened on another device, they get infected too – unless there is already installed a powerful and updated antivirus program is already installed.
Every year, these malicious computer viruses cause considerable financial harm directly or indirectly by corrupting information, causing system failure, and raising maintenance costs.
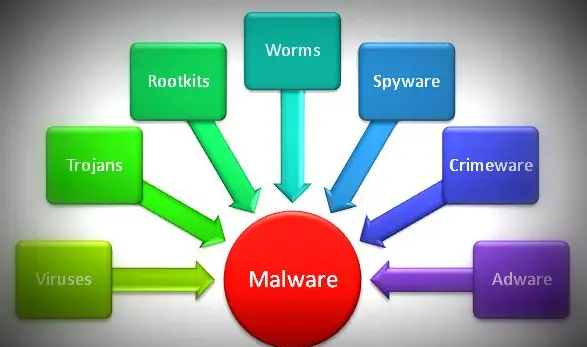
Difference Between Malware and Virus
Read this to know about Malware Vs Virus.
In a vast sense, a virus is a type of malware, and it is classified into one of the categories by the method of attack.
Types of Malware Based on Their Type of Attack
1. Virus
A computer virus works like a parasite, replicating itself infinitely or until it has completed its programmed assignment. Its purpose is to hide in an application, so the user has to activate it.
A virus is more likely to be found in an application that promotes sharing (such as email), so it can infect more systems.
A computer virus is a type of malicious computer software that replicates itself and adds its code when executed.
When the replication process is complete, this malware infects the other files and programs on your system.
These computer viruses come in a variety of types, each of which can uniquely infect a device.
We have detailed a list of viruses that commonly affect computers at the bottom of this article.
2. Worm
A lot of people are confused about the difference between viruses and worms.
A worm is capable of deleting and/or replacing something else. It aims to ruin a system as it passes from system to system. A computer worm can reproduce itself as well.
It’s autonomous, however, unlike a virus, not needing external activation. A worm can travel through networks on its own and discover fresh places to infect.
Nevertheless, a virus requires the host software.
It moves within a specified mechanism by exploiting vulnerabilities and goes through the open gate.
If left unchecked on a server, only the motion activity of the worm may cripple the bandwidth of all the host locations.
3. Trojan
A Trojan is a word used for any application that houses malware (including web applications).
Trojan malware can do what it is intended to do, but when it releases a malware attack on the system once enabled through the setup phase, it will disclose its real intentions.
Most of the time, a Trojan horse is used in devices as a backdoor.
Trojan horses generally pass as software that looks benign or innocent. Their goal is to steal data and/or provide additional access to the system.
They can also be programmed to take over the resources of systems, such as core files and the bandwidth of the network.
Be careful about .EXE or .BAT files with no custom icon or labels that appear confusing (or irrelevant)
4. Scareware
Scareware has been seen by many consumers. Unfortunately, there is sufficient awareness that it is not as large as it used to be in danger.
This malware generates an unpleasant (and sometimes flashing) alert for those who don’t understand, which appears on the screen to tell the user that their system is infected, urging them to buy the anti-malware item advertised to remove it.
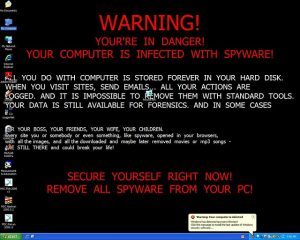
Although they do not necessarily claim that the system is infected, it is their underhanded approach that puts the danger in the first location: to scare a person into selling or installing a piece of software that can be malicious itself.
This approach can also be emulated through a website where the system is installed.
5. Spyware
Spyware is a sort of malware that hides in the background of a system and records private data such as visited locations, economic data, or keystrokes.
This data is recorded back to the creator of the malware for private use or used to communicate more personally with the infected person.
The interesting thing about spyware is that it can be used in both illegal and legal settings.
Related: Best Free Antivirus Applications For Android
6. Pop-ups and Adware
Adware is a form of malware that normally operates in combination with spyware.
It can monitor a person’s browsing or buying habits through spyware and then constantly show advertisements that frequently and irritatingly represent those habits.
However, it is not restricted to pressing sales as the adware can prompt (sometimes even force) an individual to click on an unwanted link or clearly and audibly promote pornographic content–merely as a means of embarrassment, depending on the malware creator’s agenda.
7. Ransomware
Ransomware is one of the most feared types of malware.
It takes advantage of a system vulnerability or the user downloading a Trojan file to encrypt the documents so that the system can not understand those files.
The cybercriminal then leaves a message to the system operator demanding payment–generally through some kind of untraceable cryptocurrency.
Ransomware can also behave like a worm, where it encrypts a system and requests payment, but also instantly seeks to do the same with neighbouring linked devices or spreads itself through communications from the system it affects.
Computer Virus And Its Types
Here we are trying to define computer viruses and their types based on the target of their attack. This classification of viruses does not cover all types of computer viruses.
The following are the Common Computer Viruses and their types.
1. Boot Sector Virus
This sort of virus is connected to the boot storage and will begin functioning whenever you put it on your machine.
The Boot sector contains all of the data necessary to boot the computer’s operating system. This virus either replaces the existing application or transfers itself to a different location on the disk.
This virus mainly affects floppy disks. Although they are not very prevalent today, other computer units, particularly the obsolete ones, are still causing problems.
Polyboot.B and AntiEXE are some examples.
2. Browser Hijacker
This hijacker virus can take over your browser and link to free downloads, attractive toolbars, and programs.
Moreover, the browser hijacker will open numerous fake websites that can damage your computer when you type a web address in your internet browser.
On the other hand, to keep them ahead, the most trusted browsers have built-in security to fight against these types of viruses.
3. Direct Action Virus
This sort of virus becomes active only when the infected file or program is running. Direct action viruses attack file types with extensions .exe and .com.
If it is installed in memory, it remains hidden. Non-Resident Virus is another name for it.
This virus’s primary aim is to reproduce and infect documents in folders. They typically do not delete files or impact the working efficiency and speed of the PC This virus can be detected by most anti-virus software.
4. Directory Virus
These Viruses alter the path of files. The virus program also operates in the background when you run programs infected with directory viruses.
Furthermore, once infected with file viruses, it may be hard for you to find the initial application or software.
5. Encrypted Virus
This sort of virus utilises malicious encrypted codes that make it difficult to detect antivirus software. Only when they decrypt themselves during replication can they be identified.
Since they can delete files or folders, they can have a serious impact on PC efficiency.
6. File Infector Virus
This is one of the most prevalent types of computer viruses that attaches to documents and ultimately can take over the file, totally corrupting it.
This virus also infects files or programs that can be executed. The file-infecting virus is also triggered when you run these programs, which can slow down the program and generate other harmful impacts.
This category belongs to a big block of current viruses.
7. Memory Resident Virus
Memory Resident Virus corrupts the memory of the computer and can delete documents to generate room for itself.
Resident viruses live in your system’s RAM. It can interfere with the ordinary operation of the system, which can lead to file and program corruption.
CMJ, Meve, MrKlunky, and Randex are the most common instances of resident viruses.
Related: How Can You Protect Your Phone From Smartphone Malware?
8. Macro Virus
This virus attaches macro supporting documents like Microsoft Excel or Word.
These viruses can perform a sequence of activities that affect program or software efficiency.
A virus that infects a computer by using the same macro language as the software program. Email is the primary source of such viruses.
O97M / Y2K, Bablas, Melissa. A and Relax are some examples of macro viruses. As email attachments, you may accidentally download them to your computer.
9. Multipartite Virus
This is one of the most difficult viruses to cope with as it spreads various damaging activities in several ways.
This virus may infect both the boot sector and the executable files of a machine that is already infected. If a multipartite virus hits your system, you are vulnerable to a cyber attack.
It can spread rapidly, performing in your operating system, folders, and other computer programs through unlawful activities.
They can infect the executable files as well as the boot area.
10. Network Virus
This sort of virus spreads through the Local Network Area (LAN) and the Internet. These viruses reproduce through shared drives and files.
11. Overwrite Virus
Overwrite Virus overwrites a file’s content and causes the loss of the original content. It infects folders, files, and programs as well.
The overwrite virus is one of the most dangerous viruses because it may fully delete the existing software and replace it with malicious code by overwriting it.
It can gradually replace the host’s programming code with malicious code.
You also need to get rid of your file to remove this virus. Therefore, the backup of your system files is essential.
12. Polymorphic virus
As they encrypt and alter their coding, they are very hard to identify, making it difficult to pick up your antivirus software.
Polymorphic viruses are file infectors that spread through spam and infected websites. They are complicated to detect.
They infect the system with a modified or morphed version of the current software while retaining the original code.
They can also readily replicate. Satan Bug, Elkern, Tuareg, and Marburg are among the polymorphic viruses.
13. Web Scripting Virus
In our list of computer viruses and their types, not the least but the last is the Web Scripting Virus. Unknown to you, a website may host malicious viruses added with bad intent by a third party.
These types of viruses are inserted in some links, advertisements, images, videos, and website design itself.
These can hold malicious code that will automatically download viruses or direct you to malicious websites when you click on them. Pay attention to the websites that you visit.
14. Resident Virus
It is a type of virus that hides in the computer’s memory behind an original piece of good software. When this original software stops functioning, it infects other files and applications.
This virus may easily infect other files since it is hidden in the memory and is difficult to remove from the system unless you have used efficient antivirus software.
15. Spacefiller Virus
It is an uncommon type of virus that employs viruses to fill up the blank spaces in a file. The virus is also known as the cavity virus. It does not affect the file’s size and cannot be easily identified.
Install the latest industry-leading antivirus software to keep your device secure from computer viruses.
Best Practices for Avoiding Computer Viruses
1. Keep your operating system and software up to date
Keeping your operating system and applications up-to-date is one of the easiest but most effective ways to avoid computer infections.
Software companies offer updates and fixes regularly to resolve security flaws. Staying updated ensures that your system has the most recent defensive methods against emerging threats.
2. Be cautious with email and attachments
Because email is a popular entry route for viruses, employ caution while interacting with emails and attachments.
Open attachments from unknown senders or dubious sources with caution. Before clicking on email links, mouse over them to view the actual URL.
If anything doesn’t seem right, go on the side of caution and delete the email.
3. Use strong and unique passwords
It is critical to protect your online accounts with strong and unique passwords to prevent illegal access.
A strong password should include capital and lowercase letters, numbers, and special characters. Avoid utilising popular words or readily guessed personal details.
4. Backup your data regularly
Regular data backups are a wise habit that can spare you the misery of losing data due to viruses or other unforeseen events.
To safely save your backup, use an external hard drive, cloud storage, or a mix of the two. Schedule automatic backups so that you don’t have to worry about manually storing your stuff.
With this advice and best practices, you may confidently go through the digital world, avoiding computer infections and keeping your data safe and secure.
Remember that remaining alert and proactive is essential for staying one step ahead of hackers.
Conclusion
To summarise, understanding all types of computer viruses is the first step toward protecting our digital existence.
We may considerably lower the danger of becoming vulnerable to these harmful attacks by taking proactive actions such as keeping our software up to date, maintaining safe surfing habits, and utilising dependable antivirus software.
When it comes to computer viruses, remember that prevention is always better than a cure. To maintain a safe and seamless internet experience, keep aware, educated, and protected.
Frequently Asked Questions
Creeper virus was the first computer virus, and it was a self-replicating virus that was released in 1971.
Spam is an unsolicited message(s) sent for the sender’s commercial gain. The method of delivering these messages is known as spamming.
A virus is a set of instructions that can disrupt the regular operation of your computer.
Spam messages can sometimes hold and transmit viruses.
An anti-virus is a software application that consists of tools or a collection of programs that can identify and remove all dangerous and malicious malware from your system. This anti-virus software is created in such a way that it can look through a computer’s data and detect whether files are heavily or moderately infected by a virus.
A virus infection on your computer could show itself in a variety of ways. These include unexpected system slowdowns, frequent crashes or freezes, strange pop-up warnings, unauthorised file or settings modifications, and unexpected network activity. If you see any of these symptoms, perform a trusted antivirus check to detect and remove any potential infections.
Yes, opening email attachments from unknown or suspect sources might put your machine at risk of infection. Email is a popular tool for cybercriminals to deliver malware. As a result, it is critical to be cautious when opening attachments, even if they look to be from someone you know. Always scan attachments with an antivirus tool before opening them, and avoid opening any documents that appear suspicious or strange.
While Mac computers have generally been less targeted by viruses than Windows systems, they are not immune to them. As the popularity of Macs has grown, so has fraudsters’ interest in attacking these computers. To avoid malware infections, Mac users must be cautious, follow safe browsing habits, and use trusted antivirus software.
In certain situations, with trusted antivirus software, you may be able to eliminate a computer infection on your own. More difficult or chronic illnesses, on the other hand, may necessitate the intervention of a specialist or sophisticated troubleshooting procedures. To minimise additional harm to your computer system, it is important to follow prescribed measures and seek advice from credible sources or specialists on virus removal.
We hope you are interested in this article and consider following our Facebook and Twitter pages.
Subscribe to our free newsletter so that you will get regular updates directly in your Email.
If you find this article helpful, please share it with your friends and relatives.
Subscribe to be the first to learn about new information